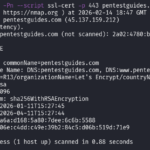
Welcome to pentestguides.com!
I post about CTF, penetration testing, bug bounty, coding challenges, fundamental knowledge, and experimentations in various cybersecurity domains as well as plain IT.
No AI.
Latest Posts
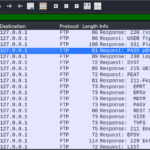
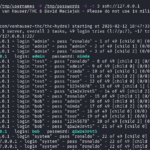
- ftp Complete Tutorial in 10 Examples – Must-know Command for CTF
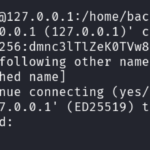
- scp Quick Tutorial – Transfer Files Securely Over SSH
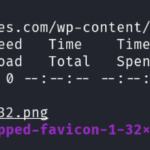
- curl Quick Tutorial – Everything You Need to Know
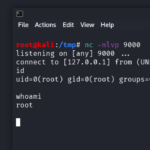
- Netcat (nc) Full Tutorial – Easy TCP/UDP Guide
- nmap Tutorial – the Ultimate Network Scanner
- Hydra Tutorial – How to Effortlessly Brute-force Network Services
- Solving Lookup – TryHackMe Challenge Writeup
- Solving Basic Pentesting – TryHackMe Challenge Writeup

- RootMe Writeup – Full TryHackMe CTF Solution
- Corridor Writeup – TryHackMe IDOR Challenge

- Lo-Fi Writeup on TryHackMe – File Inclusion

- TryHackMe TakeOver Writeup – Subdomain Challenge
- TryHackMe “Agent T” Writeup – Easy Challenge

- TryHackMe Compiled Challenge – Writeup

- Lazy Admin Writeup – TryHacKme Challenge

- wafw00f – Detect WAF (Web Application Firewalls)
- whatweb Tutorial: Identify Website Technologies

- Pickle Rick Writeup – Easy TryHacKme CTF

- Neighbour Writeup – Easy IDOR TryHacKme Challenge

- Solving The Suspicious Domain – Hack The Box challenge
.
Read posts from a tag
arbitrary file read backdoor binary brute forcing bug bounty bug bounty cheatsheet clash of code cms code golf ctf curl dns ffuf file transfer find ftp hackerone hackthebox hydra idor intigriti kali linux linux linux command nc nmap penetration testing pentest pentesting php privilege escalation python reconnaissance reverse shell scp sftp smb ssh sudo suid tcp tls tryhackme udp web
Disclaimer
All content published on this website is for educational purposes only.
The techniques, tools, and methodologies described here are intended to be used only on systems you own or have explicit permission to test.
I do not encourage or take responsibility for any illegal use of the information provided.
