CTF & Bug Bounty » Hack The Box » HTB Challenges » Spookifier – Very Easy HTB Challenge
ReactOOPS is a very easy challenge on Hack The Box, designed to teach us how to exploit the recent critical unauthenticated RCE (remote code execution) named “React2Shell” (CVE-2025-55182).
Click here to solve ReactOOPS on Hack The Box
Table of contents
Solving ReactOOPS – Exploiting React2Shell
Hack The Box describes the challenge as follows:
NexusAI’s polished assistant interface promises adaptive learning and seamless interaction. But beneath its reactive front end, subtle glitches hint that user input may be shaping the system in unexpected ways. Explore the platform, trace the echoes in its reactive layer, and uncover the hidden flaw buried behind the UI.
We are given the source inside ReactOOPS.zip.
After downloading and extracting the project folder, we quickly spot something interesting in the package.json file:
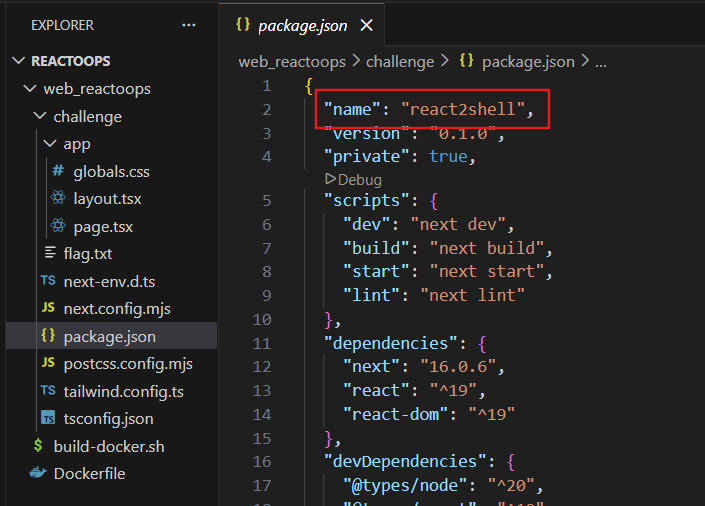
(I use Visual Studio Code in the screenshot)
The website is vulnerable to the infamous React2Shell exploit (CVE-2025-55182).
After reading this blog post, I came across this perfect Python POC on Github.
After downloading the Python script and installing the “requests” dependency, we quickly retrieve the flag executing the “cat /app/flag.txt” command:
C:\>py poc.py http://94.237.49.209:55552/ "cat /app/flag.txt"
500
0:{"a":"$@1","f":"","b":"s8I48LfEDhqpCdFN5-HbU"}
1:E{"digest":"HTB{jus7_1n_c4s3_y0u_m1ss3d**************************************************************************************}"}Yes, I did it on Windows.
Conclusion – React2Shell too obvious?
Clearly, we don’t need to know anything about React or the vulnerability in order to get the flag.
Just reading the code and looking for “react2shell” online gives us all we need.
I feel like it wasn’t necessary to use the name “react2shell” in the package.json file, it gives away the whole challenge.
But anyway, it was great exploiting it for real with an easy POC.
Read more Hack The Box CHALLENGES WRITEUPS on pentestguides.com!
Disclaimer
This article is provided for educational purposes only.
All techniques demonstrated were performed in a controlled lab environment.
Do not attempt to reproduce these actions on systems you do not own or have explicit authorization to test.
I do not encourage or take responsibility for any illegal use of the information provided.
