Pentest Methodology » Pentest Tools » Web – Pentest Tools
Web apps are the most common targets in CTF and Bug Bounty.
Tools will help us do many things:
- Enumerate subdomains, headers, parameters, filenames, extensions, directories, endpoints, authentication, tokens, etc.
- Help us mapping the web applications
- Taking screenshots of the web applications
- Automate exploits
- Inspect requests
- Act as a proxy
- etc.
Latest Web Tools Covered
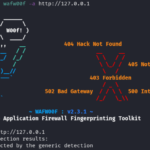
- wafw00f – Detect WAF (Web Application Firewalls)
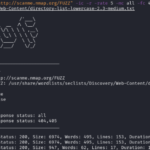
- whatweb Tutorial: Identify Website Technologies

- Fuzz Websites with ffuf – Complete Tutorial
.
Disclaimer
All content published on this website is for educational purposes only.
The techniques, tools, and methodologies described here are intended to be used only on systems you own or have explicit permission to test.
I do not encourage or take responsibility for any illegal use of the information provided.
