CTF Writeups & Bug Bounty » Try Hack Me » THM Challenges » Compiled THM Challenge – Writeup
In this short post, we are going to solve the Compiled challenge from TryHackMe by finding the flag inside the strings of a compiled program.
» Link to the challenge on TryHackMe
Table of Contents
Introduction – Compiled
The only instructions are the following:
Download the task file and get started.And the description of the challenge is the following:
Strings can only help you so far.Besides this information, the flag pattern is *********_****, so 9 characters, an underscore, and 4 characters.
The file we download has a .Compiled extension.
Let’s see what we can do with the strings…
Retrieving the flag from strings
strings in this context usually refer to the plaintext words we can extract from a compiled program.
The strings command is available in Linux, however because I was not on Linux when doing this, I searched for a strings extractor online and ended up on this website:
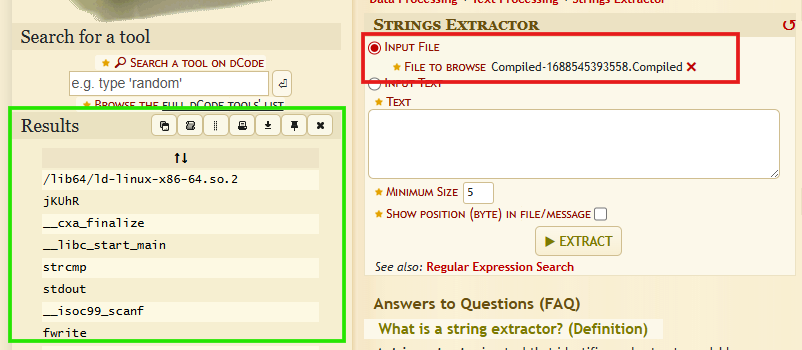
I uploaded the .Compiled file (red box) and the extracted strings appear on the left column (green box).
Among the many results, we can find strings that seem to belong to a piece of code that tests a password against a value:
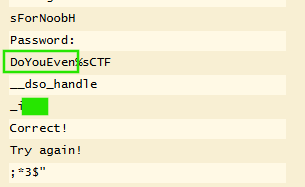
Remember the flag pattern? It needs 9 characters, then an underscore, then 4 characters.
The first green box shows a suspicious text made of 9 letters, then %sCTF that we will conviniently ignore.
Two lines under it, we see a text that starts with an underscore and contains 4 letters.
Well, after trying, the flag is indeed the combination of those 2 values.
Flag:
DoYouEven_i***The final letters are blurred to encourage you to do it yourself!
Final Thoughts – Compiled
This challenge was easy but it’s a good introduction to the strings command and how strings might be revealed and extracted from a compiled program.
We got a bit lucky on the flag…
Read more THM Writeups on pentestguides.com:
- Solving Lookup – TryHackMe Challenge Writeup
- Solving Basic Pentesting – TryHackMe Challenge Writeup
- RootMe Writeup – Full TryHackMe CTF Solution
- Corridor Writeup – TryHackMe IDOR Challenge
- Lo-Fi Writeup on TryHackMe – File Inclusion
Disclaimer
This article is provided for educational purposes only.
All techniques demonstrated were performed in a controlled lab environment.
Do not attempt to reproduce these actions on systems you do not own or have explicit authorization to test.
I do not encourage or take responsibility for any illegal use of the information provided.